Cyber Security
Cybersecurity giant Trellix has disclosed a significant security incident involving unauthorized access to a portion of its source code repository. The company confirmed the breach in an official statement published on its website, stating it immediately engaged...

Cyber Security
A sophisticated cybercriminal operation dubbed “AccountDumpling” has compromised approximately 30,000 Facebook accounts worldwide. Discovered by Guardio Labs, this Vietnamese-linked campaign abuses Google’s AppSheet platform to bypass traditional email security...
Cyber Security
Wireshark, the world’s most widely used open-source network protocol analyzer, has released a major security update addressing over 40 vulnerabilities, several of which enable arbitrary code execution through malformed packet injection or malicious capture files....
Cyber Security
A high-severity access-control vulnerability (CVSS 8.2) in Cursor, a widely used AI-powered coding environment. The flaw uncovered by LayerX has allowed any installed extension to access a developer’s API keys and session tokens secretly. This results in total...
Cyber Security
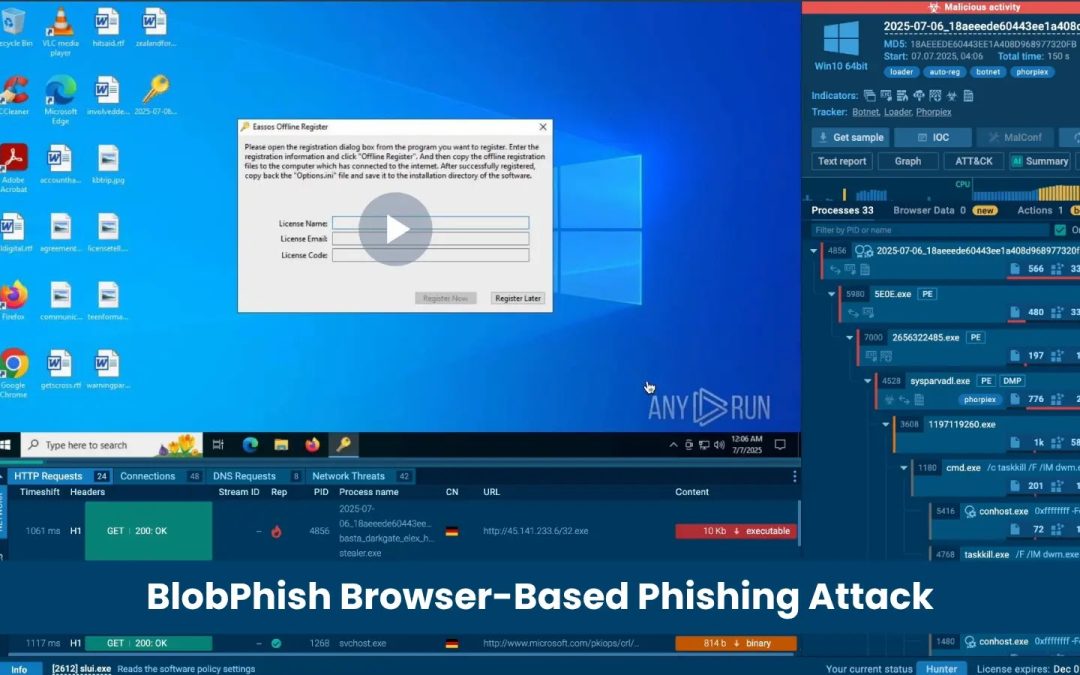
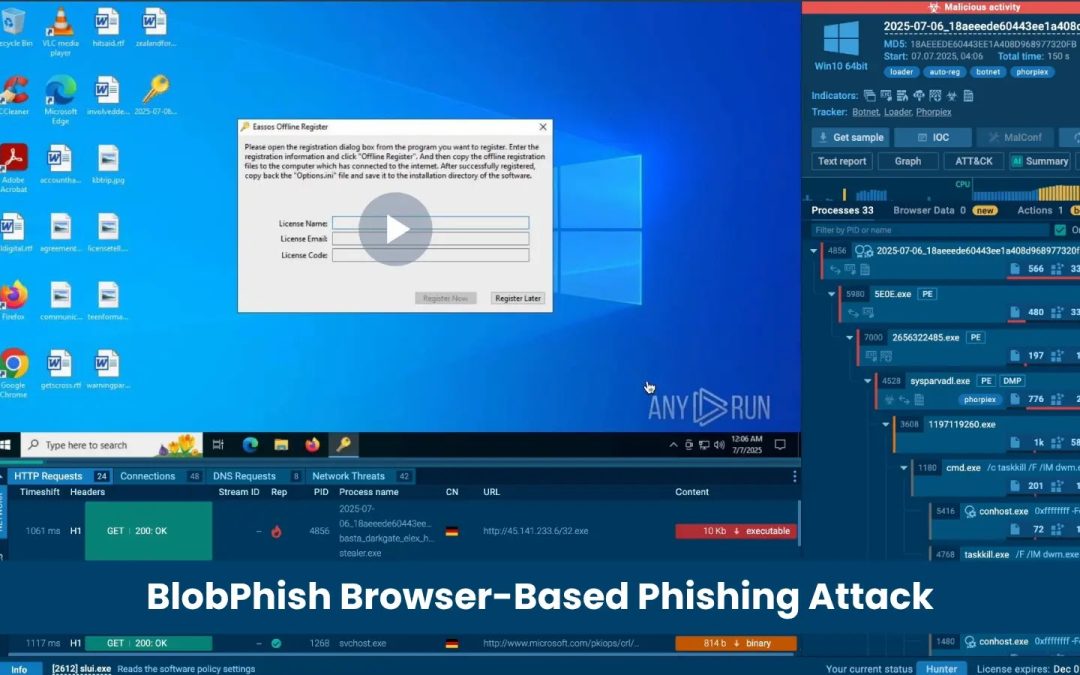
A sophisticated, memory-resident phishing campaign called BlobPhish, active since October 2024, that exploits browser Blob URL APIs to silently steal credentials from Microsoft 365 users, major U.S. banks, and financial platforms while remaining almost completely...
Cyber Security
A new fake document reader app found on the Google Play Store has been silently installing Anatsa, a powerful Android banking trojan, on thousands of user devices. The malicious application surpassed 10,000 downloads before Google removed it, putting a significant...