Cyber Security
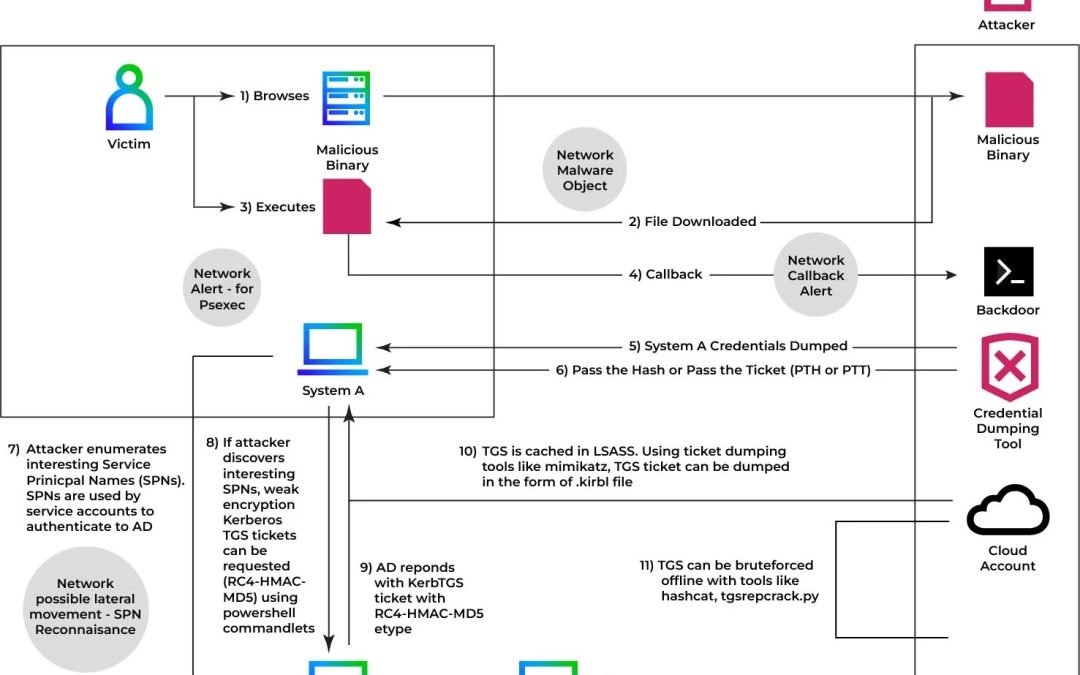
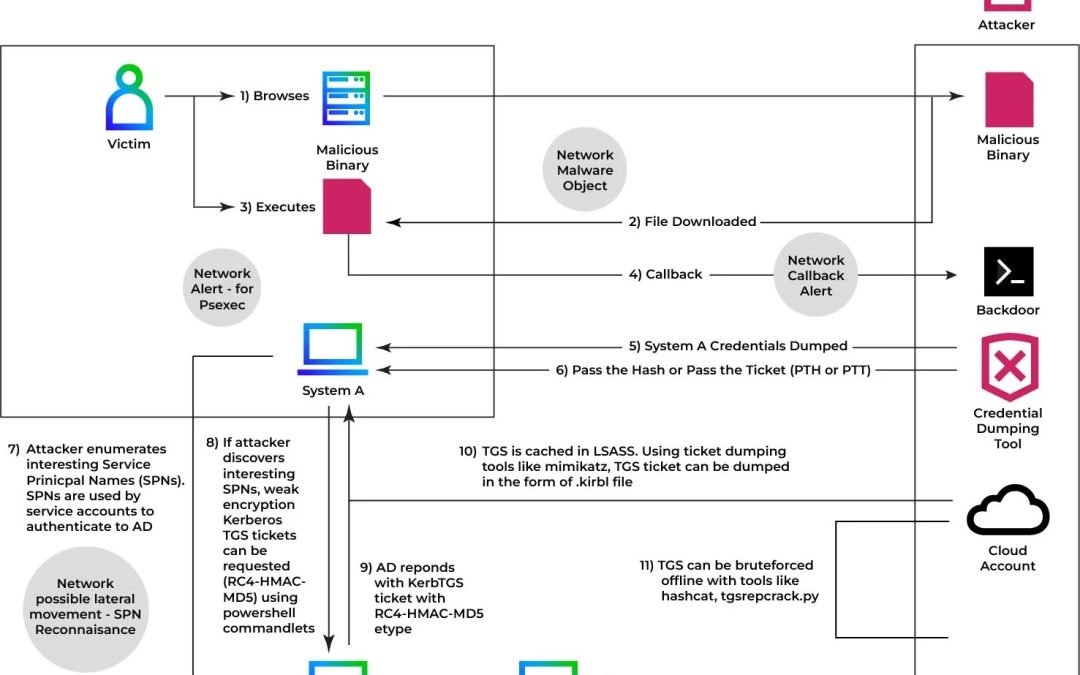
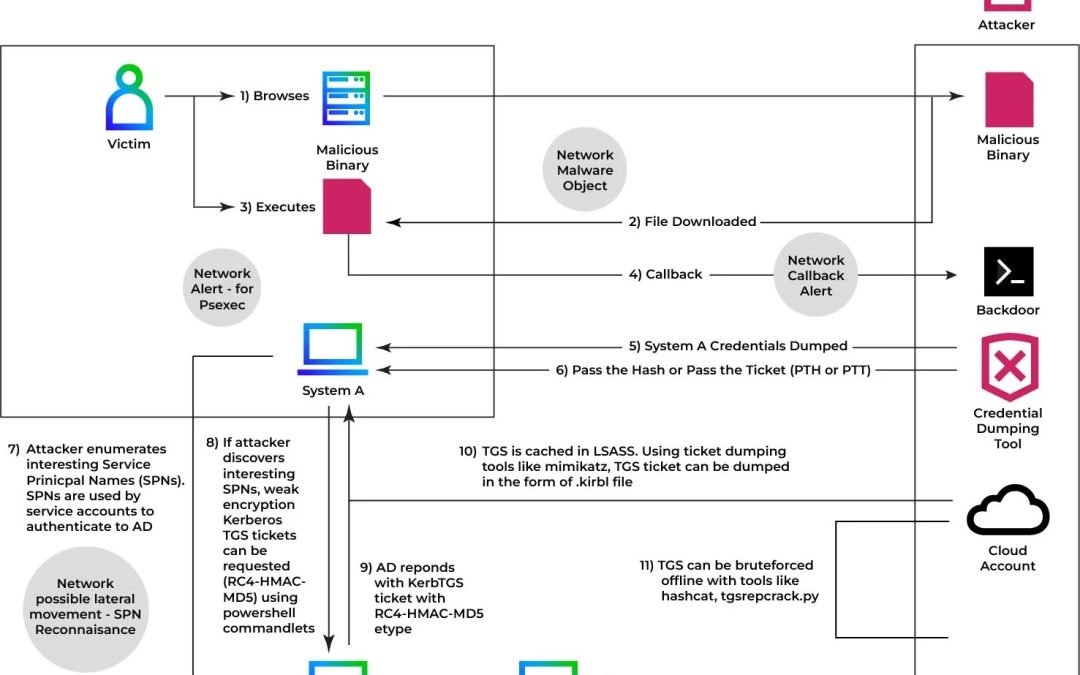
“`html An advanced iteration of Kerberoasting referred to as the “Ghost SPN” assault enables attackers to gather Active Directory credentials while eliminating all evidence of their operations, making conventional detection frameworks largely oblivious to the...
Cyber Security
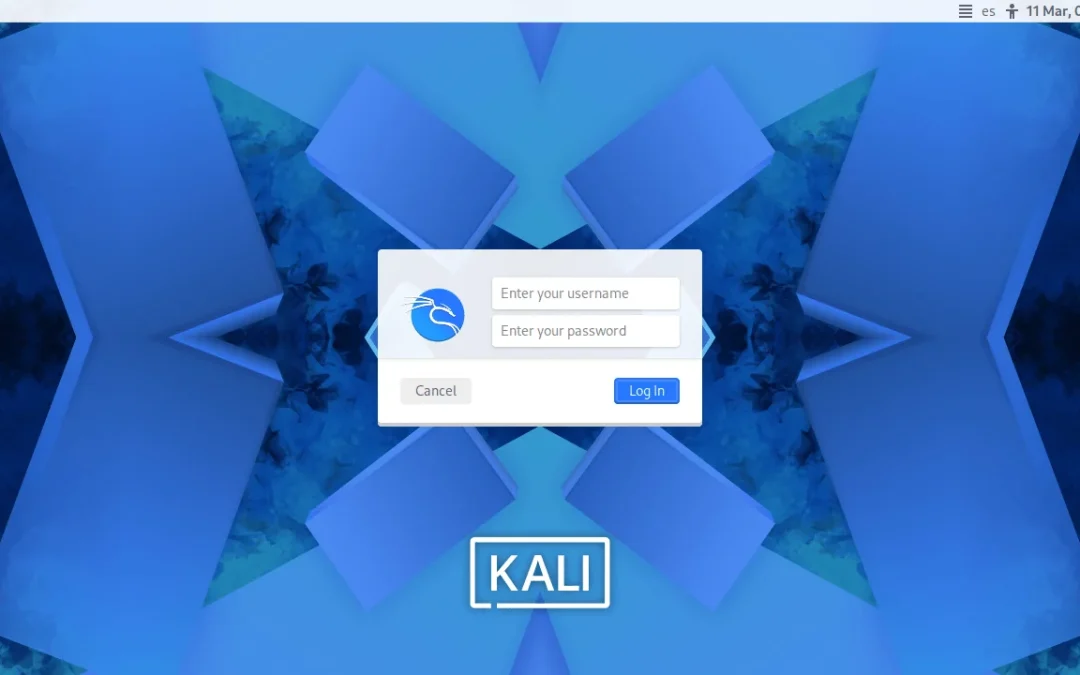
“`html Kali Linux 2026.1 has been officially launched, signifying the initial significant enhancement of the year for the widely used penetration testing distribution. Created for specialists involved in technical security investigation and vulnerability...

Cyber Security
“`html A considerable attack vulnerability concerning outdated Microsoft Internet Information Services (IIS) servers. On March 23, 2026, during Shadowserver’s daily network evaluations, researchers discovered more than 511,000 End-of-Life (EOL) IIS instances...

Cyber Security
“`html An adversarial actor is said to have extracted around 100 GB of personally identifiable information (PII) from Crunchyroll, the anime streaming behemoth owned by Sony, following access via a compromised employee at its outsourcing associate, Telus. The...

Cyber Security
“`html Malicious Script Injection in Trivy Compromise A complex supply chain breach targeting the official Trivy GitHub Action (aquasecurity/trivy-action) has breached continuous integration and continuous deployment (CI/CD) pipelines worldwide. Revealed in late...

Cyber Security
“`html FBI, CISA Warn Russian Hackers The Federal Bureau of Investigation (FBI) along with the Cybersecurity and Infrastructure Security Agency (CISA) have recently published a collaborative advisory concerning a widespread phishing operation. This warning...