Our Blogs
Top 10 Ransomware File Decryptor Tools for 2025
Tools for decrypting ransomware files are crucial in retrieving data that has been encoded by malicious software without having to pay any ransom....
Session Hijacking: A New BitM Attack Allows Hackers to Steal User Sessions Instantly
An advanced cyberattack method known as Browser-in-the-Middle (BitM) has surfaced, empowering malicious actors to circumvent multi-factor...
Alert: CISA Issues Warning on Windows NTFS Vulnerability Exploitation Threat
The CISA heightened its cybersecurity warning by including six critical Microsoft Windows vulnerabilities in its Known Exploited Vulnerabilities...
“Cutting-Edge Malware Analysis Tools: Top 10 Picks for 2025”
Essential tools for dynamic analysis of malware are crucial in identifying and comprehending present-day online dangers. These utilities operate...
“Beware of Clipboard Hijacking: Protect Your Data from Fake CAPTCHA Attacks”
Uncovered by cybersecurity experts, a sophisticated cyberattack chain known as "KongTuke" is targeting unsuspecting internet users through...
Essential Cybersecurity Solutions for Safeguarding Remote Devices in 2025
The surge of remote work has significantly expanded the attack surface for cyber attackers, underscoring the heightened importance of robust...
Secure Remote Desktop Connection with Incognito Mode for Complete Anonymity
Microsoft's Remote Desktop Protocol (RDP) has unveiled an obscure yet pivotal security attribute informally termed as "incognito mode" utilizing its...
Exploiting DLL Side-Loading Vulnerability in Google Chrome: An Inside Look at Threat Actors Executing Malicious Payloads
There is a new attack vector that cybersecurity experts have identified, in which threat actors are exploiting a vulnerability found in Google...
Urgent Alert: Cisco IOS XR Software Vulnerability Allows for DoS Attacks
Cisco has released security notifications regarding various vulnerabilities impacting its IOS XR Software, focusing primarily on a notable memory...
Exploitable Kibana Vulnerability Allows Attackers to Run Arbitrary Code
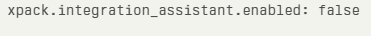
Elastic has published an urgent security alert regarding a crucial weakness in Kibana, dubbed as CVE-2025-25012, which permits authenticated...
Discover security vulnerabilities on your web applications and networks