An advanced cyberattack method known as Browser-in-the-Middle (BitM) has surfaced, empowering malicious actors to circumvent multi-factor authentication (MFA) and snatch user sessions in just a few seconds.
This strategy leverages web browser features to seize authenticated sessions, presenting a notable danger to establishments depending on conventional security protocols.
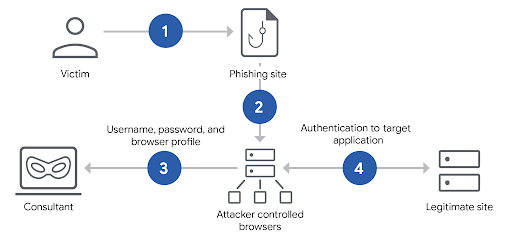
BitM assaults emulate authentic browsing encounters by directing targets through a browser controlled by the attacker. When a user accesses a suspicious website or clicks on a phishing link, their activities are channeled through a proxied browser managed on the attacker’s server.
This browser replicates the appearance of the valid site, deceiving targets into inputting credentials and completing MFA tests. Following authentication, the attacker seizes the session token preserved in the browser, effectively confiscating the user’s authorized status.
Essential Aspects of BitM:
- Invisible Proxies: Programs like Evilginx2 or Delusion (Mandiant’s internal utility) serve as mediators between the target and the victimized service. These proxies modify HTTP responses to substitute valid domains with phishing domains, facilitating the extraction of session tokens.
- Quick Deployment: Unlike traditional hidden proxies requiring extensive tailoring, BitM frameworks like Delusion enable operators to quickly focus on any site. Functions like Firefox profile storage and automated load balancing simplify large-scale phishing ventures.
- Live Observation: Perpetrators can monitor target engagements in real-time, facilitating immediate capture of sessions upon successful authentication.
BitM attacks are especially perilous as they sidestep MFA, a shield many organizations view as their ultimate barrier. By seizing session tokens, malicious actors secure continuous entry to accounts without the need for the victim’s credentials again, as confirmed by Google here.
This tactic proves effective against apps leveraging virtual desktop infrastructure (VDI) or cloud amenities, where session hijacking can offer access to restricted networks.
- Enterprise Security Threats: BitM may result in security breaches, theft of intellectual property, or complete takeovers of Active Directory. Red teams frequently employ these tactics to evaluate organizational fortifications, exposing flaws in MFA dependence.
- Velocity and Expansiveness: The simplicity of employing BitM utilities such as Delusion’s capacity to enlarge containers and manage initiatives via tags facilitates extensive assaults. Victims may remain unaware of the breach until it’s too late.
Though no system is entirely invulnerable, institutions can alleviate BitM risks through layered security:
- Hardware-Based MFA (FIDO2): Security keys like YubiKey or Google Titan enforce cryptographic challenges bound to specific domains. Malicious actors cannot replay FIDO2 responses across various sites, thwarting BitM exploits.
- Client Certificates: Connecting authentication to device-specific certificates thwarts session reuse on unauthorized devices. This approach complements FIDO2 to prevent token hijacking1.
- Behavioral Surveillance: Tools detecting unusual login patterns or deviations in browser fingerprints can flag potential BitM compromises.
- Security Education Sessions: Training users to identify phishing endeavors (e.g., dubious URLs or unsolicited authentication requests) remains pivotal1.
BitM symbolizes a substantial shift in cyber hazards, utilizing browser features to dodge traditional security tactics. The promptness and efficiency of this attack necessitate immediate attention from security teams worldwide.
The post New BitM Attack Lets Hackers Steal User Sessions Within Seconds appeared first on Cyber Security News.