Cisco has released security notifications regarding various vulnerabilities impacting its IOS XR Software, focusing primarily on a notable memory corruption issue within the Border Gateway Protocol (BGP) confederation implementation.
The identified vulnerability, known as CVE-2025-20115 and possessing a CVSS rating of 8.6, presents the possibility for unauthorized remote attackers to instigate denial-of-service scenarios on compromised network infrastructure.
The flaw associated with the BGP confederation (cisco-sa-iosxr-bgp-dos-O7stePhX) results from memory corruption that is triggered when a BGP update incorporates an AS_CONFED_SEQUENCE attribute with 255 or more autonomous system numbers.
This buffer overflow vulnerability, categorized as CWE-120, represents a significant peril to network steadiness for enterprises leveraging Cisco IOS XR with configured BGP confederation.
Vulnerability in Cisco IOS XR Software
According to the security advisory from Cisco issued on March 12, 2025, malefactors can exploit this vulnerability by dispatching crafted BGP update messages to trigger memory corruption. This corruption could compel the BGP process to restart, resulting in a network-wide denial of service situation.
To successfully exploit this vulnerability, the attacker needs to manipulate a BGP confederation speaker within the same autonomous system as the target or partake in a network configuration where the AS_CONFED_SEQUENCE attribute naturally exceeds the specified size limit.
The vulnerability affects all versions of Cisco IOS XR Software that have BGP confederation enabled, spanning from versions 7.11 and earlier, 24.1 and earlier, to 24.2 up to version 24.2.20.
| Risk Factors | Details |
| Impacted Products | Cisco IOS XR Software 7.11 and earlier, 24.1 and earlier, as well as 24.2 up to version 24.2.20. |
| Impact | Complete denial of service |
| Prerequisites for Exploitation | Malefactor must exercise control over a BGP confederation speaker situated within the same autonomous system as the victim |
| CVSS 3.1 Score | 8.6 (High) |
Countermeasures
Cisco has published software updates to rectify this vulnerability. Enterprises utilizing affected versions of IOS XR are advised to upgrade to either version 24.2.21 (upcoming release), 24.3.1, or 24.4, which remain unscathed.
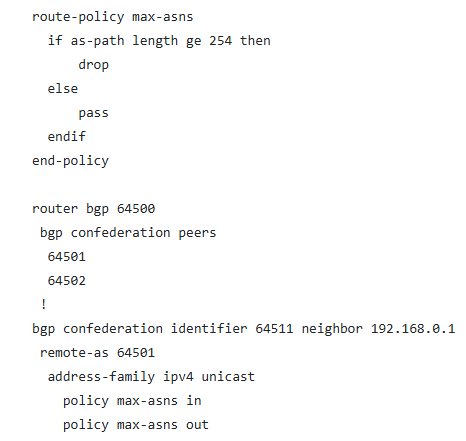
For entities unable to promptly perform updates, Cisco has introduced a workaround that limits the BGP AS_CONFED_SEQUENCE attribute to 254 or fewer AS numbers through a routing policy aimed at discarding BGP updates with extended AS path lengths on confederation peers.
The implementation of this policy necessitates the creation of a max-asns route policy, subsequently applying it to BGP neighbors:
Subsequently, this policy should be implemented in the BGP neighbor configurations utilizing the “policy max-asns in” and “policy max-asns out” directives.
Network administrators can identify the vulnerability by inspecting BGP confederation configuration utilizing the “show running-config router bgp” command. If “bgp confederation peers” appear in the output, the device might be susceptible.
The Cisco Product Security Incident Response Team (PSIRT) has reported no documented malevolent exploitation efforts thus far.
Enterprises operating on affected versions are urged to apply the necessary updates promptly or employ the provided workaround to restrict the BGP AS_CONFED_SEQUENCE attribute to 254 or fewer AS numbers.
The article Cisco Warns of IOS XR Software Vulnerability That Let Attackers Trigger DoS condition first appeared on Cyber Security News.